Reviewfacility.eu
Introduction
Reviewfacility.eu was an initiative by the European Commission's DGCNECT bootstrapped in the very early days of the SARS-CoV-2 pandemic. Both governments and health institutions and society were grappling with an urgent need to deal with the immediate effects and many uncertainties of a viral pandemic - the potential scale and fallout of which was unknown. Technology was looked at for immediate relief, but this immediately evoked dystopian images. Techno-optimism on the one hand and at the same time serious and well-argued concerns within civil society with regards to privacy, and security: obviously a situation with a more than average risk of tone-deaf technology push that could result in broad resistance and lack of adoption due to lack of transparency and proportionality. With the wealth of expertise and reusable open source components already available within the community of the Next Generation Internet initiative, it made sense to tap into that - and stimulate the open source approach that was central to the vast majority of initiatives.
The focus of reviewfacility.eu was orthogonal to the epidemological and healthcare angle: its mission was to help mature the technology in question from multi-disciplinary points of view (e.g. security, accessibility, privacy analysis, protocol verification) - whether this concerned complete mobile contact tracing apps, components used (like the custom base45 decoder or log4j), the European Federation Gateway Service (EFGS) for interoperability of national contact tracing solutions, or the EU Digital COVID Certificate Gateway (DGCG) which was developed to share validation and verification information across all national backend servers. These efforts were looked at from a purely technical point of view, the intent was not to evaluate whether contact tracing has lived up to its promised or served its intended purposes from a epidemological or scientific point of view.
| Protocols | Apps and projects | Reviews |
| DP-3T (FR) | STOP COVID (FR) | Security quickscan of base45-decoder of the European Federation Gateway Service (public) |
| Google-Apple Exposure Notification Framework (GAEN) | Corona Warn-App (DE) | In-depth security assessments of the Google- and Apple-components of the GAEN-framework |
| BlueTrace (SG) | Simmel BlueTrace | Security quickscan of BlueTrace (public) |
| TCN (NL) | CoronaMelder (NL) | Security assessment of the CoronaMelder-app |
| DESIRE (FR) | COVIDSafe (CH) | Quickscan log4j in code Digital COVID Certificate (DCC) Gateway (public) |
| ROBERT (FR) | ProteGO Safe (PO) | High-level security assessment of the ProteGO-app (private) |
| Immuni (IT) | High-level security assessment of the Immuni-app (private) | |
| WCAG accessibility evaluation HOIA app | ||
| In-depth assessment of the European Federation Gateway Service (public) | ||
| In-depth assesment of the Digital Covid Certificate (DCC) Gateway - part 1 | ||
| In-depth assesment of the Digital Covid Certificate (DCC) Gateway - part 2 |
The dependency on proprietary technologies showed up as a disruptive factor, and something to address in policy. The fact that most member states felt compelled to adopt the GAEN framework after a while - sometimes instead of well-contructed solutions already produced by their own researchers and technologists - is indicative of that dependency. It is a tell-tale sign when some of the largest economies on the planet have no other way to enable integration with the dominant Google and Apple mobile platforms than to surrender in full. By making the switch to a controversial solution only available to the customers of these two vendors they actually abandoned the users of other mobile operating systems, such as the European mobile ecosystems SailFish, UBPorts and postmarketOS. From the point of view of reviewfacility.eu, this problem of societal exclusion and push towards dominant market players was brought to the table but of course could not be solved. To this day, there are still no contact tracing or covid certificate solutions available to these citizens.
Overview of the work done
The reviewfacility.eu project was started in April 2020, during the first lockdown and in the center of the cambrian explosion of new explorative open source technologies. Over the lifetime of the project, emphasis shifted from supporting a wide spectrum of smaller open source technologies produced by a broad developer community to pragmatically dealing with the more consolidated and top-down setup that evolved later on.
A number of open source tracing apps received technical scrutity with short and effective scans on security aspects and accessibility. The following reports present the work done within the context of these apps:
- 3.1 High-level assessment: BlueTrace (ROS)
- 3.2 High-level assessment: ProteGO-app (ROS)
- 3.3 High-level assessment: Immuni-app (ROS)
- 3.4 WCAG evaluation HOIA-app (Accessibility Foundation)
While the security assessment of the Dutch CoronaMelder-app performed by Radically Open Security was not direct part of the review facility effort, its channels were used to conduct and coordinate the research at the request of the Netherland government.
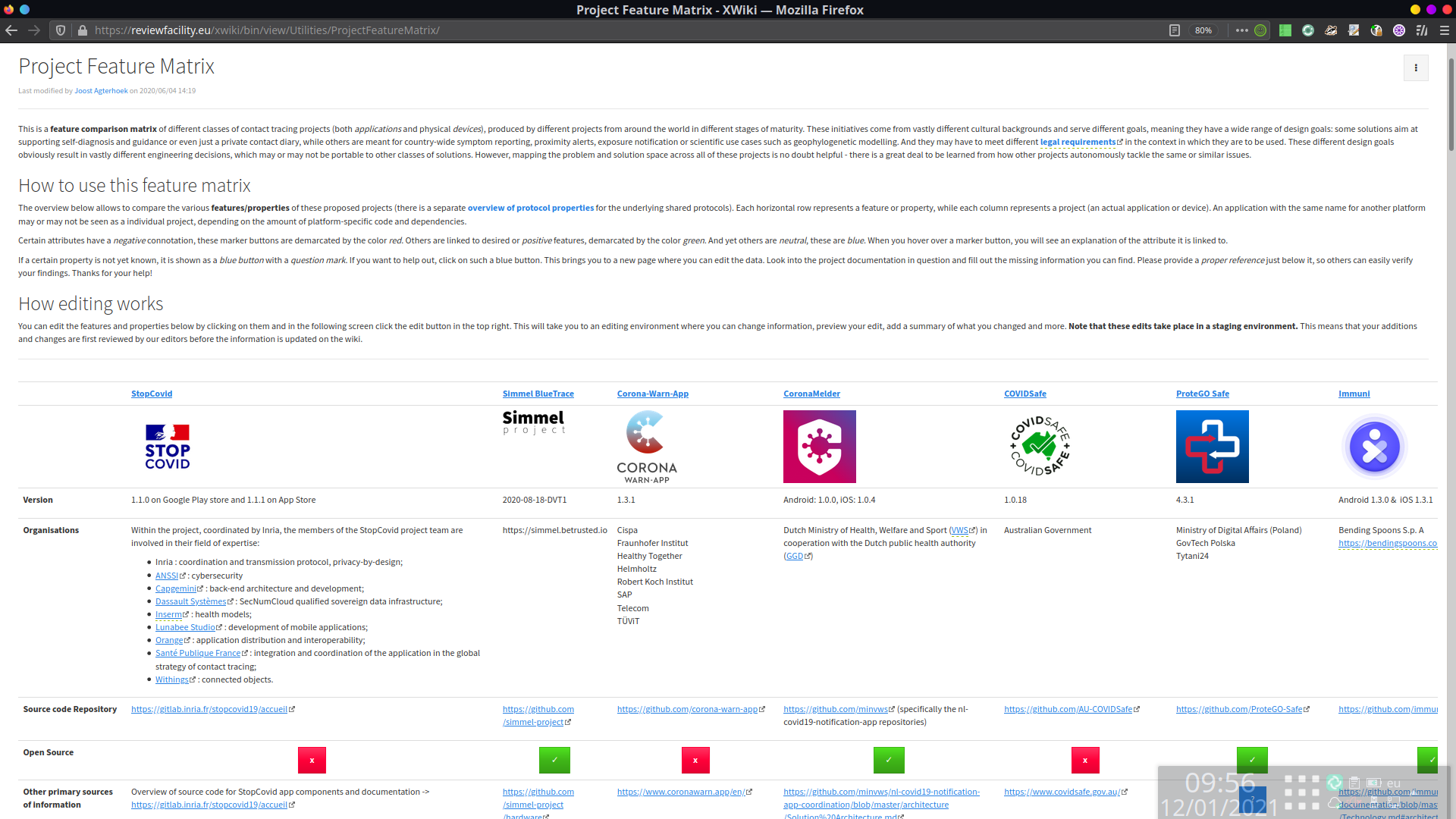
In the second phase reviewfacility.eu focused on in-depth analysis of a much more restricted set of technologies that had meanwhile emerged. The team verified both implementations of the Google/Apple Exposure Notification (GAEN)-framework for contact tracing, and zoomed in on the technical and organisational infrastructure to share and verify digital certificates across countries to enable travel and commerce in a sustainable, safe way.
The following reports provide more detail on the various findings:
- 3.5 In-depth assessment of the European Federation Gateway Service (ROS)
- 3.6 In-depth assessment Digital COVID Certificate (ROS)
- 3.7 High-level assessment: base45decoder (ROS)
- 3.8: High-level assessment: log4jcheck (ROS)
- 3.9: In-depth assesment of the Digital Covid Certificate (DCC) Gateway pt 1 (ROS)
- 3.10: In-depth assesment of the Digital Covid Certificate (DCC) reference implementation (ROS)
- 3.11 In-depth assessments Google and Apple Exposure Notification (GAEN) framework: Apple
While significant effort was put into the research on the Google/Apple Exposure Notification (GAEN)-framework for contact tracing and in particular the implementation of Google and Apple, at the end of reviewfacility.eu there is still relevant work to be executed in this area. The early decision of many national governments and health agencies to switch from autonomous solutions - which like for instance involved using dedicated hardware tokens independent from smartphones, like in the case of BlueTrace and Simmel - and accept a complete dependency on the GAEN-framework for contact tracing continues to result in hard to resolve issues with transparency and verifiability.
Security research on these implementations was only possible on (incomplete) available source code and, after lengthy negotiation and discussion, on implemented and currently running technology with specific restraints and requirements. One of the key open questions remains the "Exposure Notification Express" feature - which is present in many millions of devices produced by Apple but wholly undocumented in the source code released by said vendor. Further in-depth analysis of this hidden component is still needed.
The in-depth security assessment of the Google-implementation of GAEN identified issues in the published code, but not on running programs on tested devices. Test devices were identifiable, as the Google-implementation of Bluetooth-powered contact tracing differed from the protocol specification, possibly allowing identification of persons. Privacy assessments by the Testing Apps for COVID-19 Tracing (TACT)-project from Trinity College Dublin indicate that the reliance of the Google-implementation of GAEN on the Google Play-service required collection of personal data that was 'extremely troubling from a privacy viewpoint'.1
The inquiry into the European Federation Gateway Service (EFGS) for interoperability of national contact tracing solutions, and later the EU Digital COVID Certificate Gateway (DCC) proved fertile and productive from the start. Obviously, there were less hindrances and complications as indicated before because these efforts were developed in their entirety as open source - although in a cautious way, with batch public releases made from a privately administered repository in the cloud. A respectable amount of security issues were discovered, although no major problems or vulnerabilities that could be exploited by a malicious outsider with large impact. Some of these issues did affect vendors and their current products, such as the HTTP Desync attack which resulted in Symantec having to issue a security advisory (internal number SVM21-022, the fix for this HTTP smuggling vulnerability was released in ProxySG 7.3.7.1 on February 17 2022. It was published by NIST in the NVD as CVE-2021-46825).
European Federation Gateway Service
The European Federation Gateway Service is the pan-European solution to allow national backends of contact (or proximity) tracing apps to upload keys of newly infected people and download diagnosis keys from the backends of other participating countries. The EFGS was initiated and designed by Deutsche Telekom (T-Systems) and other contributors and has been made available under an Apache 2.0 open source license.
The implementation of the EFGS draws on and adds to the document 'European Proximity Tracing An Interoperability Architecture' and the document 'European Interoperability Certificate Governance' of the eHealth Network, a voluntary network of European national authorities on digital health. The repository offers details on the dataflow from and to national backends, (third-party) dependencies and requirements to build the system and backend technology expected to be in use.
Digital Green Certificate Gateway
The Digital Green Certificate Gateway was designed to exchange different kinds of information to support the validation of the vaccination status, test result, or recovery status of people across European countries. For this purpose an EU Trust Framework was designed that introduces a standardized signed data structure, represented as a 2D code (QR). To validate this data structure in each country, cryptographic public keys are distributed using the DGCG, which acts as a trust anchor. The architecture of the DGCG is inspired by the design of the EFGS. The DGCG was again initiated and designed by Deutsche Telekom (T-Systems) and other contributors and has been made available under an Apache 2.0 open source license.
Reviewfacility was involved by DG CNECT from before the first public release of the gateway efforts, up to the most current release at the end of the project. There were no extreme privacy and security issues found at the time of reviewing, but the code was significantly improved because of the feedback delivered. Most identified issues had to do with differences in and problems with the design and source code of the gateway and the actual implementation, as well as the lack of certain data authentication and verification measures. One high threat level finding2 in one of the reference implementations concerned insufficient verification of data authenticity for uploaded cryptographically protected messages to the gateway, and an elevated threat level finding was that the HTTP server stack was vulnerable to an HTTP desynchronization attack. Of course lack of verification of data coming from other countries, or various other components in the system, is not an issue if it is assumed that member states do not act maliciously and the official DGC gateway is being used. However, not everyone may have the luxury of those benevolent assumptions, so the better option is to avoid these risks altogether by addressing design weakness, avoiding anti-patterns, restrict the scope to reduce risks, etc.
Conclusion
As the reports produced by ReviewFacility.eu indicates, emergency technology crafted to assist with tackling the pandemic does benefit from transparency and outside scrutiny. The technologies behind contact tracing are certainly not flawless, and in the wrong hands might cause societal harm at scale. As Aleid Wolfsen, chairman of the Netherlands DPA Autoriteit Persoonsgegevens stated: "Nobody wants to become a walking antenna with a permanent link to the government".3
Reviewfacility.eu covers a unique period in modern European history, when the threat of a pandemic pushed national governments and health institutions to develop and implement technologies for widely used contact tracing and vaccination certification. The various approaches and technical implementations to do this were documented and reviewed in detail in the open, collaborative environment that the review facility provides, inviting contributions and input from a worldwide community of privacy, security, ethics and open source experts, including the Next Generation Internet research and development community.
We believe that reviewfacility.eu played a positive and constructive role by establishing a shared understanding of the problem space, establishing a technological baseline and promoting best practices. The developers of the Netherlands' corona app CoronaMelder publicly stated that the comparative analytical work of Reviewfacility.eu was a major technical inspiration and that they had taken the feature analysis framework from the project and had adopted it as a whole as their design requirements. Subsequently the app gained a reputation as a best practise in various contexts, also outside of the domain of contact tracing - as a poster child of the 'open source first' approach.
The GAEN-technologies offered national governments and health agencies an easy to deploy and widely used basis for contact tracing instead of the wild diversity of earlier designs and protocols. But this convenience had a clear price: there are underlying security and resilience risks when there is a dependency on proprietary technology that is opaque to all but a single entity. It is a market reality that such technologies are being used at scale, but piggy-backing on them as a government for critical tasks in a sensitive domain (and tracking the location of citizens is such a domain) does result in loss of transparency and ultimately no longer being in control of ones own destiny.
Within the limitations of reviewfacility.eu it was not possible to open these black boxes entirely, given both technical and legal constraints. The role of reviewfacility.eu was made significantly more difficult because of the partially closed nature of the GAEN implementations. The evaluations carried out by reviewfacility.eu did shed some highly desirable light onto these implementations, enough to understand that there are actual risks and that significant further research is needed. More work is needed, but this will need to happen outside of reviewfacility.eu.
Another area in which reviewfacility.eu worked was in looking at the collective mechanisms through which European member states were to exchange and access each others information. In this administrative domain and the international data coordination layer, the societal and political stakes are just as high. The political pressure behind contact tracing and digital vaccination certificates did not make this job easier.
The technical side of such an endeavour is complex by its very nature, but the risk surface is additionally enlarged because of the international framework, the variety of stakeholders and actors and differences in maturity and approach. Each member state has their own risk assessment and mitigations in place, and even small differences between those can lead to unwelcome situations. The work of reviewfacility prompted noteworthy improvements to improve the baseline situation for all, and while many of the issues identified might only be exploitable by authenticated users, the fact that these authenticated users are spread across organisations and countries makes prevention worthwhile - not to mention that there is always the possibility of human error during administration.
Reviewfacility was able to provide substantive analysis and support capacity to those carrying the heavy responsibililty of executing the policies under high time pressure, having to turning plans and constraints into implementations and running code. Privacy and security issues were identified with differences in and problems with the design and architecture, with the actual implementation at the level of source code and dependencies, but also occasionally with a lack of data authentication and verification measures.
Coda
The presence of closed and proprietary solutions, such as the technologies of Apple, Google Play and Symantec/BlueCoat, was challenging given the"open by default" model driving the Next Generation Internet initiative - and these proprietary aspects led to most of the unresolved issues. Beyond the technical work which was significantly complicated by lack of access to the full technical stack and complete source code, even just navigating the legal paperwork cost significant amounts of time - involving lots of back and forth with legal departments of these companies over a period of many months.
The free and open source approach did prove its value where within the project the beneficiaries of our support were themselves open source, creating an open and transparent framework for collaboration with an open-ended community - and facilitating unrestricted external scrutity with interested and knowledgeable stakeholders and partners. We therefore recommend that policy makers across Europe continue to more broadly put in place regulations and tender requirements to transition their entire technology stack to free and open source software and hardware, and to promote the broad societal adoption of this technology. This will greatly simplify future interventions like reviewfacility.eu, lower costs, improve security through transparency and help Europe to have more technical autonomy.
Data Controller Responsibility
The open approach that allowed self-registration of community members involved processing personal information. For the purpose of Article II.9.1 of EU Regulation 2018/1725 of the European Parliament and of the Council of 23 October 2018:
- the data controller for Reviewfacility.eu is the Head of the Unit "Administration & Finance", Directorate "Resources & Support", Directorate-General for Communications Networks, Content and Technology
- the data protection notice is available at https://ec.europa.eu/info/data-protection-public-procurement-procedures_en.
The privacy statement states that the Data Controller should only keep IP addresses for the time necessary for the duration of the browsing session. Retention of visitor log files was bound to a maximum duration of one year.
Per July 1st 2022, the three services (reviewfacility.eu, participate.reviewfacility.eu and forum.reviewfacility.eu are all terminated, taken offline and erased. All log files and all user interaction are erased as well.
Recommendation on legislative revision
One of the critical outcomes of the project was that the legal basis for reverse engineering for technical security analysis by users and stakeholders in Europe is currently very problematic indeed. White hat security research on proprietary technology is impossible to conduct in a legal manner, even at the request of the European Commission or of national governments - and even in cases where these is an clear discrepancy between what the vendor states and the observable truth. This legal barrier not only directly threatens the security researchers themselves, but more importantly it blocks security improvements based on such research. Since attackers don't care about copyright, we feel this is an extremely important issue to solve before the next unknown crisis hits.
-
https://www.scss.tcd.ie/Doug.Leith/pubs/contact_tracing_app_traffic.pdf↩︎
-
Throughout the reports on security assessments, vulnerabilities or risks are labeled and categorized according to the Penetration Testing Execution Standard (PTES): http://www.pentest-standard.org ↩︎
-
https://www.nporadio1.nl/nieuws/binnenland/ddebfa08-5284-4600-b1f4-a7fe925c53c6/privacywaakhond-over-corona-app-burger-geen-wandelende-antenne-in-contact-met-overheid↩︎
Acknowledgements
NGI Emergency Tech Review Facility was operated by NLnet and Radically Open Security under contract nr: LC-01499045 with the European Commission.




