FTEproxy
FTE enables developers to build systems resistant to surveillance and censorship.
fteproxy provides transport-layer protection to resist keyword filtering, censorship and discriminatory routing policies. Its job is to relay datastreams, such as web browsing traffic, by encoding streams as messages that match a user-specified regular expression.
- The project's own website: https://fteproxy.org/
Network communications are increasingly becoming the target of surveillance and censorship. One natural defense is to use traditional cryptographic protocols — traditional encryption incurs low-overhead and does a good job of providing privacy. However, because encryption is so effective, many governments (e.g., Iran, Pakistan, and China) are willing to block state-of-the-art cryptographic protocols such as TLS and SSH.
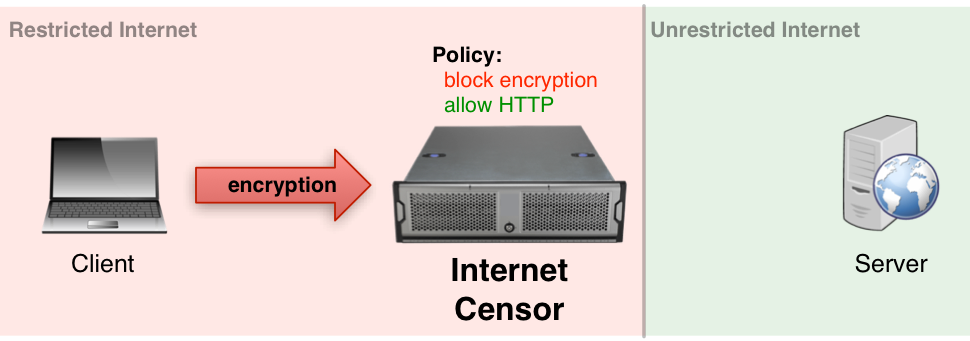
Figure 1: A government can easily identify that a client and server are using an encryption protocol, and refuse the connection.
Our Solution: Format-Transforming Encryption
Format-Transforming Encryption (FTE) is a novel cryptographic primitive that extends traditional encryption. Traditional cryptographic primitives take a key and a message as input, and output an unformatted ciphertext. FTE takes a key, message and format (a compact set descriptor) as input and outputs a ciphertext in the format set. As an example, a format may describe the set of valid messages from an uncensored protocol, such as HTTP.
The software that realizes Format-Transforming Encryption, fteproxy, bootstraps FTE to relay arbitrary data streams. fteproxy uses regular expressions to describe and transmit messages from an uncensored protocol (e.g., HTTP), but may actually be relaying a censored protocol (e.g., Tor, TLS, SSH, etc.) To a government, traffic looks like HTTP, even though it may actually be a censored protocol.
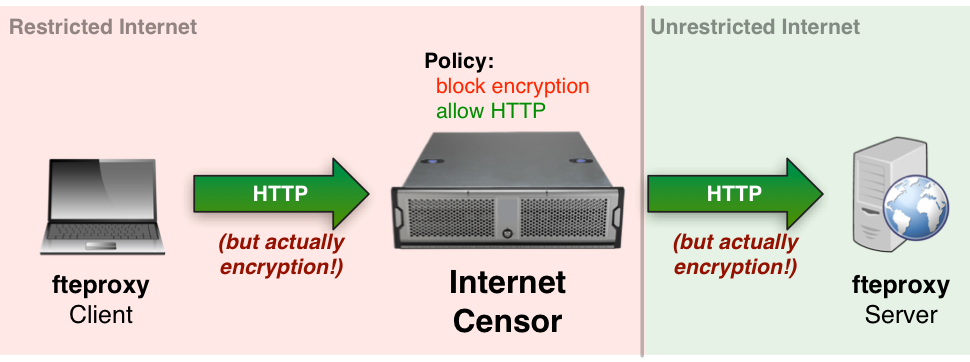
Figure 2: fteproxy transparently encrypts communications such an uncensored protocols looks like a censored protocol.
Kevin P. Dyer

